SiliVaccine, a North Korean anti-virus application for Windows, includes elements of code lifted from an anti-virus engine produced by Japan’s Trend Micro, according to a detailed analysis of the software by researchers at computer security company Check Point.
The software also deliberately fails to alert the user if a specific piece of malware is detected and came bundled with a piece of malware.
The researchers examined a copy of SiliVaccine 4.0 that was sent to me in 2014. The software came in via an email that contained a link to a zip file on Dropbox. The sender claimed to be “Kang Yong Hak,” a software engineer in Japan, but within hours of the email being received, the mailbox associated with it had been closed.
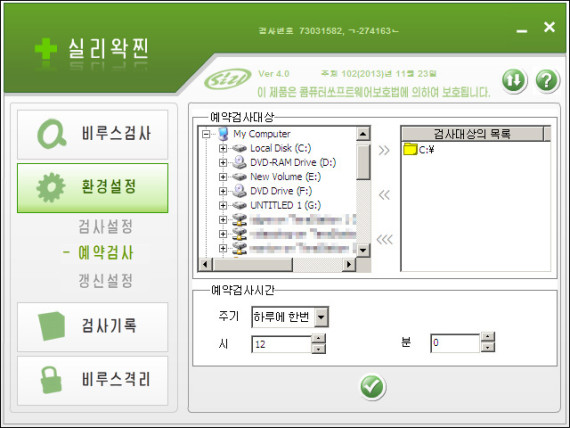
A screen from SiliVaccine, a North Korean anti-virus application. (Photo: North Korea Tech)
The software was mentioned in a recent Bloomberg News story about North Korean hackers with a link to my original story and that’s when Check Point researcher Mark Lechtik contacted me to get a copy.
Lechtik and colleagues performed a forensic analysis of the software and determined that large chunks of the anti-virus engine were an exact match to a 10-year old engine from Trend Micro, a major computer software company with headquarters in Tokyo.
The code wasn’t a complete copy, but there was enough similarity to determine North Korean engineers had probably started with the Trend Micro engine and made some custom modifications to it.
Further analysis of the code revealed a hard-coded white listing for a malware signature named by Trend Micro as “MAL_NUCRP-5,” which is a family of malware. That means that whenever SiliVaccine detects this group of malware, it passes right by and doesn’t remove it or alert the user.
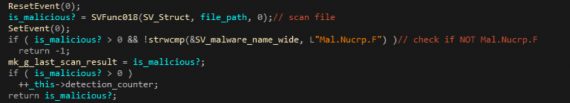
Code in SiliVaccine to ignore malware. (Photo: Check Point)
The nature of the malware and what it does is unclear but, as Lechtik noted, “what is clear is that the North Korean regime does not want to alert its users to it.”
Technically, it would make more sense to just remove the malware’s signature from the pattern library but the North Korean engineers didn’t do that. That’s probably because they didn’t have the ability to rewrite Trend’s signature files.
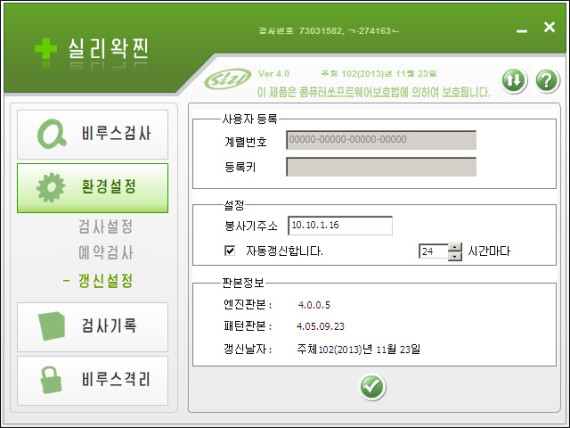
A screen from SiliVaccine (Photo: North Korea Tech)
One other thing of note from the file: the copy I received came bundled with a copy of the “JAKU” malware. JAKU forms a botnet and is usually spread by sharing BitTorrent files, said Lechtik. It has been observed targeting and tracking specific individual victims in both South Korea and Japan, including members of International Non-Governmental Organizations (NGOs), engineering companies, academics, scientists and government employees, he said.
The JAKU file in the software contained an electronic signature of “Ningbo Gaoxinqu zhidian Electric Power Technology Co., Ltd,” a Chinese organization that signed files attributed to the “Dark Hotel” hacker group. Dark Hotel has been previously associated with North Korea.
The big question is how SiliVaccine came to include code from Trend Micro. Check Point provided the SiliVaccine copy to Trend Micro, which examined it and didn’t disagree with the conclusion on code similarity.
“While we are unable to confirm the source or authenticity of that copy, it apparently incorporates a module based on a 10+ year-old version of the widely distributed Trend Micro scan engine used by a variety of our products,” the company said in response.
But said it is equally in the dark about how the code got there.
“Trend Micro has never done business in or with North Korea. We are confident that any such usage of the module is entirely unlicensed and illegal, and we have seen no evidence that source code was involved. The scan engine version at issue is quite old and has been widely incorporated in commercial products from Trend Micro and third party security products through various OEM deals over the years, so the specific means by which it may have been obtained by the creators of SiliVaccine is unknown,” it said.
Trend added that as the engine is so old, there is no material risk to current customers.
Lechtik and colleague Michael Kajiloti will also be presenting details of the findings on May 23 at Caro Workshop, a computer security conference in Portland, Oregon.



Kang Yong Hak looks like Korean name. How can you say he/she is “a software engineer in Japan”?
In the email I received, the sender wrote “I am a software engineer in Japan.”