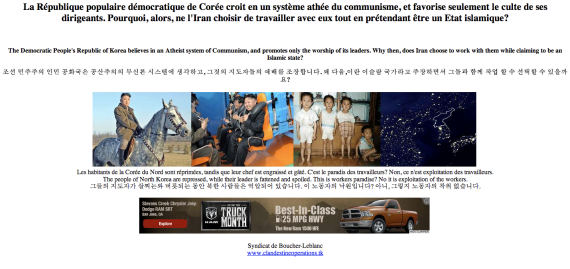
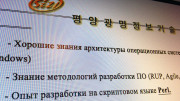
The website of Nosotek, the foreign-North Korean software programming joint venture, has been hacked. The site was hit sometime late Sunday or early Monday and its front page was replaced with a message in French, English and Korean attacking North Korea. [This story has been updated. Please see below.]
“The Democratic People’s Republic of Korea believes in an Atheist system of Communism, and promotes only the worship of its leaders. Why then, does Iran choose to work with them while claiming to be an Islamic state?”
Underneath were a couple of pictures of Kim Jong Un, one of him on a horse and another at an amusement park, alongside a photo of malnourished children and the famous nighttime satellite photo showing North Korea in darkness next to a bright South Korea and China.
Another trilingual message followed:
“The people of North Korea are repressed, while their leader is fattened and spoiled. This is workers paradise? No it is exploitation of the workers.”
And before the bottom of the page an advertisement served by Google’s ad network, which on my screen was looked a little bizarre as it promoted the Dodge Ram pick-up truck.
The website isn’t hosted in North Korea. It’s one of many that are hosted on servers overseas. In Nosotek’s case, the company is using a server operated by Neue Medien Munich in Germany.
A tag on the page claimed the hack was the work of “Syndicat de Boucher-Leblanc.” A linked website entitled “Global Clandestine Operations Network” has information in English, French, Russian and Arabic, but offers little information about the group.
As of time of writing, the group has not returned a request for comment.
Here’s what it looked like:
UPDATE: A reader writes to note, “the French text is definitely not written by a French native. Too many obvious mistakes even a 10 year old would not make. it is Google translated. but then, why put the French text in front, with the biggest font? PS. Korean version is google translated too.”
UPDATE 2: The hacker who attacked the site appears to also be posting online under the name “Free Syrian Navy.” The PayPal donate button on the linked Clandestine Operations site links to an account held by “[email protected].”
Further, the Google AdWords account (pub-0189838191925575) used on the hacked page is the same as that used on the Clandestine Operations site. It’s also the same one used on a Free Syrian Navy Blogspot page. The associated Blogspot profile doesn’t add any additional information about the user.
The AdWords account was also added to a Wikipedia page in an attempt to promote a fourth website, go-college.webs.com, by a user calling themselves “Assed206.” The page now redirects to the Clandestine Operations home page.
There’s also a Global Clandestine Operations Network Facebook page that lists the mission as, “We provide anonymous communication and secure browsing tools to help fight terrorism and global violence!”
And a Twitter feed @clandestinenet.
UPDATE 3: The Nosotek website is now returning an error message. The hacked content has gone, but the main site is yet to return.

Here my reaction on Twitter:
@felixabt Now state-sponsored hacking of websites of legitimate North Korea businesses? Part of more intense psychological war? More http://www.facebook.com/ACapitalistInNorthKorea?ref=hl