Will Scott, a computer scientist from Washington state, just returned from several months as a guest lecturer at the Pyongyang University of Science and Technology (PUST).
In an interview with North Korea Tech and in posts on Reddit, Scott spoke about what it’s like to be at PUST.
This is part two of a three-part series. Part one published yesterday covered life at PUST and part three looks at North Korea’s Red Star Linux.
When PUST was first proposed, the school said it was intending to use a satellite Internet connection. If that ever did happen, it’s not connection in use now.
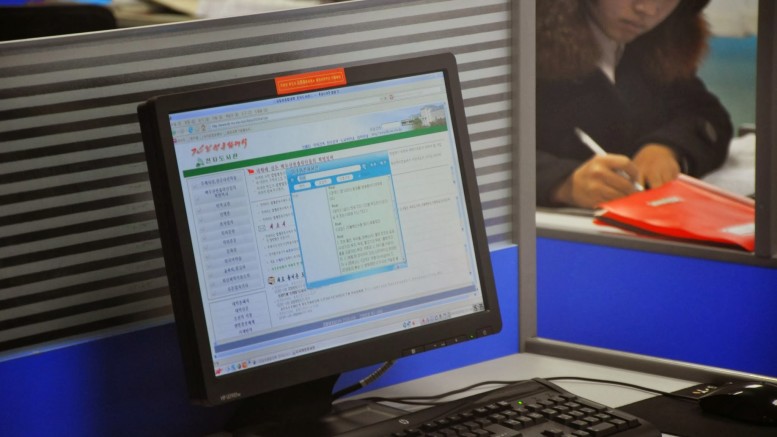
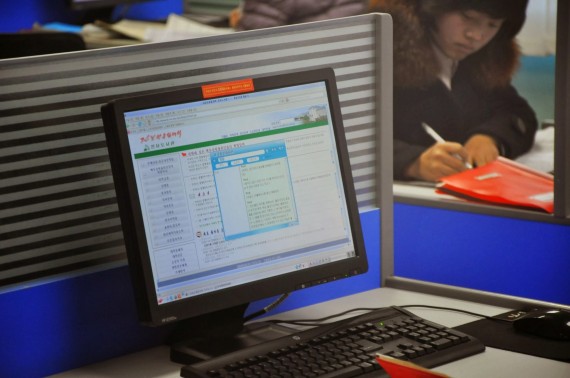
PUST has a link to the domestic Internet connection that connects Pyongyang via China to the rest of the world. It hosts a handful of websites based in the capital and is believed to be available to a handful of officials, companies, ministries and other official organizations in North Korea. Access is likely closely restricted and monitored.
“We theoretically had a T1 (1.5Mbps) line as a campus to the hub downtown,” said Scott. “In practice it varied from getting 1Mbps upload and download to unusably slow. It’s unclear where the bottleneck was though.”
PUST advises lecturers to make a new email account before heading to North Korea, in part for security and in part to reduce the amount of email they would otherwise be receiving.
Scott says he took that advice, but judges the SSL encryption employed by Google on connections to Gmail would have kept the content of his messages secret anyway.
“The main security I felt was that I wasn’t typing my normal password while there,” he said.
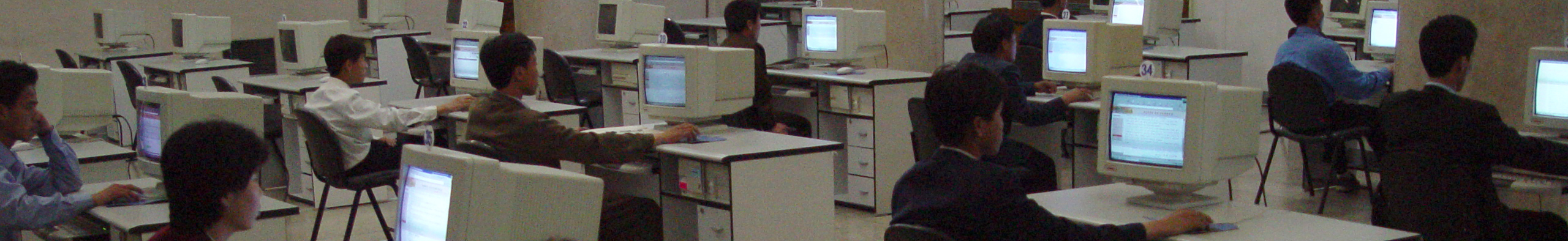
In addition to lecturers, some students also enjoy Internet access at PUST.
“The graduate students have it, the undergrads don’t,” he said. “Our faculty are pushing to allow the senior undergrads to have access. At schools connected to the intranet, it sounded like that was available to both grads and undergrads — some of our grads had been at Kim Il Sung University or Kim Chaek University previously and had experience with the intranet.”
For some of the time he was there, Scott used a Google Chromebook. Ir runs on Chrome OS, which relies heavily on software that runs on Google’s servers so it’s more secure from viruses and worms than Windows, Linus and Mac OS computers.
But worms — pieces of computer code that replicate themselves from machine to machine and steal data — were prevalent.
That’s because students relied on USB memory sticks to transfer files to avoid the uncertain and uneven availability of the Internet. The USB sticks provide an easy way for the worms to copy themselves.
Scott said he examined a few, but they didn’t appear to be particularly insidious.
“The ones I looked at were pretty boring,” said Scott. “Known Windows worms.”

The domain name system used on the Internet is explained in this poster at the Pyongyang University of Science and Technology (Will Scott)
As for censorship, Scott says he didn’t experience anything that appeared to be done by the North Korean government.
“The Internet is not filtered, because access is controlled at the physical rather than technical level,” he said. “That being said, at our university we had a squid HTTP proxy between us and the Internet connection that kept a log of everything visited.”
But he did find some sites off limits.
“The only things I noticed blocked were when U.S. sites blocked my computer due to my DPRK IP address.”
One such site was that of Oracle, the major California-based maker of enterprise database software and the company that owns the Java software that runs on most PCs.
“You can’t read the mysql documentation off of their site,” he said. “That being said, you can download it from the Ubuntu mirrors so it’s not particular effective, but it caused questions from some of the students.”