Cyber attacks against South Korean organizations have been much in the headlines in recent weeks. With each attempt to crash a web server, phish for private information or infiltrate a computer in South Korea, the country’s government points its finger of blame towards North Korea, but concrete evidence is often thin on the ground.
Investigators will typically try to trace a cyber attack by discovering the IP (Internet protocol) address from which it originated. Every computer on the Internet has such an address and discovering the source address will typically help identify the organization or service provider network from which the attack was launched.
But tracking cyber attacks is a difficult job at the best of times — attackers don’t often use their own machines but those of other people that they control through malware. In some cases they will route traffic through numerous points so it’s difficult to trace all the way back to source, and in other cases will use fake IP addresses to divert attention elsewhere.
Perhaps the North Korean hackers aren’t skilled enough to cover their tracks, so the source IP addresses can be easily caught, maybe they want the source to be clear, or perhaps North Korea is being implicated by hackers in other countries and the South Korean government is a little too eager to blame its neighbor. Without more technical information, it’s impossible to know.
There are two blocks of IP addresses that can be readily identified as North Korean.
The first is a block of 1,024 addresses that was put into use in 2010 by Star Joint Venture, the Internet service provider venture between the state-run Korea Posts and Telecommunications Co. and Thailand’s Loxley Pacific.
This is used to house all the official North Korean websites, such as KCNA, Naenara, the Voice of Korea, and Rodong Sinmun. Computers in North Korea capable of accessing the global Internet, such as those owned by resident foreigners, also use addresses in this range.
The block runs from 175.45.176.0 to 175.45.179.255.
A second, lesser known block of addresses also exists.
It contains 256 addresses and runs from 210.52.109.0 to 210.52.109.255.
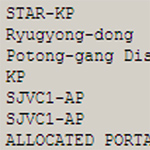
Here’s what you get when you query the addresses in the “whois” directory:
inetnum: 210.52.109.0 - 210.52.109.255 netname: KPTC country: CN descr: Customer of CNC admin-c: TC254-AP tech-c: TC254-AP status: ASSIGNED NON-PORTABLE changed: [email protected] 20040803 mnt-by: MAINT-CN-ZM28 source: APNIC
At first glance they appear to be Chinese addresses because they are owned by China Netcom, one of China’s largest Internet service providers. But a closer look reveals they are assigned to a customer called KPTC. That’s Korea Posts and Telecommunications Co., the government-run telco.
The addresses were previously used for several North Korean websites and related Internet services including the Chesin e-mail system. Most of the services have moved to the Star JV addresses, but at least one website still uses the Chinese addresses: Chosun Expo.
They are still in use for other purposes. Scanning sometimes reveals blank or test websites that appear and disappear within a day, and there are at least three routers connected through the addresses behind which there are likely additional PCs.



Year’s ago I was the target of an Attack named “I love You ” I was using Black Ice Defender. An Active Firewall that not only blocked but reverse raced the attack. I was using Windows 98 and at least one year post its release. This hack was successful in scamming $600 million from US institute’s but was stopped a few days after I had my own attack a probable attempt to turn my computer into a Zombie. All prior knowledge of the origin was South West China North of the Philippine Islands The origin of this was manila and the IP returned in my trace was that of Manila. I did have that data within a split second of being attacked. Black Ice Was able to penetrate the Spoof software used and Find not only the IP but the Mac addresses of al of the Computers linked to the Router at the time of the attack. For some reason Active Firewalls were made illegal as an infringement of privacy. Any computer in the act of sending at that time had to have its defences DOWN and I was able to obtain such data It should be logical to use an advanced Active Firewall . We need to be able to penetrate the Software used to HIDE IP addresses. its on the computer itself. Such software can be purchased for $29 to 39 on the net Legally. time to alter the laws to enable us to respond and perhaps shut these Dweebs down.